Rhino Ransomware Spotlight
Summary
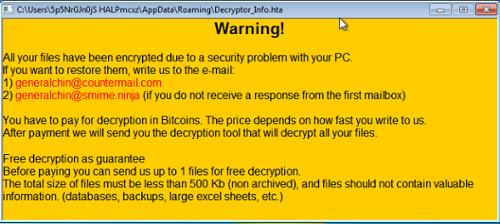
Rhino Ransomware is a new malware, first identified in April 2020, which has been analyzed by VMRay Labs in their blog. The latest sample (of which was the basis for analysis) was discovered by Twitter user @GrujaRS on May 4th.
Overview
Rhino Ransomware is one of the latest in ransomware analyzed by VMRay Labs. The ransomware carries several capabilities including, disabling services, hindering backup recovery, deleting shadow copies, and persistence. The first step of infection disables several Windows Security and Defender services, as well as Windows Update service, and error reporting. Additionally, the ransomware attempts to stop Microsoft Exchange, sqlserver, and sqlwriter. Stopping these services leads the researchers to believe the targeted victims could be businesses. The next step is the deleting of shadow copies and the backup catalog, as well as Windows Recovery Mode. Persistence is achieved through a registry entry and copying itself to the %AppData% directory as mshtop32bit.exe. After file encryption, a file marker "Marvel01 is added. An email address is included in the ransom email note. Excluded file types are .EXE, .SYS, .LNK, .DLL, .MSI, and the ransomware's notes. Further details can be found in the report located within the Reference section below.
Recommendations
- Ensure anti-virus software and associated files are up to date.
- Search for existing signs of the indicated IoCs in your environment.
- Consider blocking and or setting up detection for all URL and IP based IoCs.
- Keep applications and operating systems running at the current released patch level.
- Exercise caution with attachments and links in emails.
Reference
https://www.vmray.com/cyber-security-blog/rhino-ransomware-malware-analysis-spotlight/

 Greek
Greek